Always remember to plan ahead. It wasn’t raining when Noah built the ark.
~Richard Cushing
Despite the upcoming Industrial Revolution 4.0, where technology is set to rise to greater heights, there exist only minuscule probabilities of predicting natural disasters. The onslaught of a natural disaster has no bounds as it takes a heavy toll on our livelihoods. Another unfortunate victim of said disasters is data.
Disasters cause damage to infrastructure that is home to data servers and storage facilities. This results in the loss of precious and timeless data gathered over the years and is thus irreplaceable. While mankind had UNICEF, FEMA, and WHO in the event of disasters, data Samaritan was the introduction of disaster recovery.
What is Disaster Recovery?
Disaster recovery involves the strategies deployed to ensure that data is revivable and secured at off-site locations in the occurrence of an untoward event like natural disasters, cyber-attacks, etc. Disaster recovery includes two main components:
- Data Replication
- Computation / Computer Processing when the primary server is down
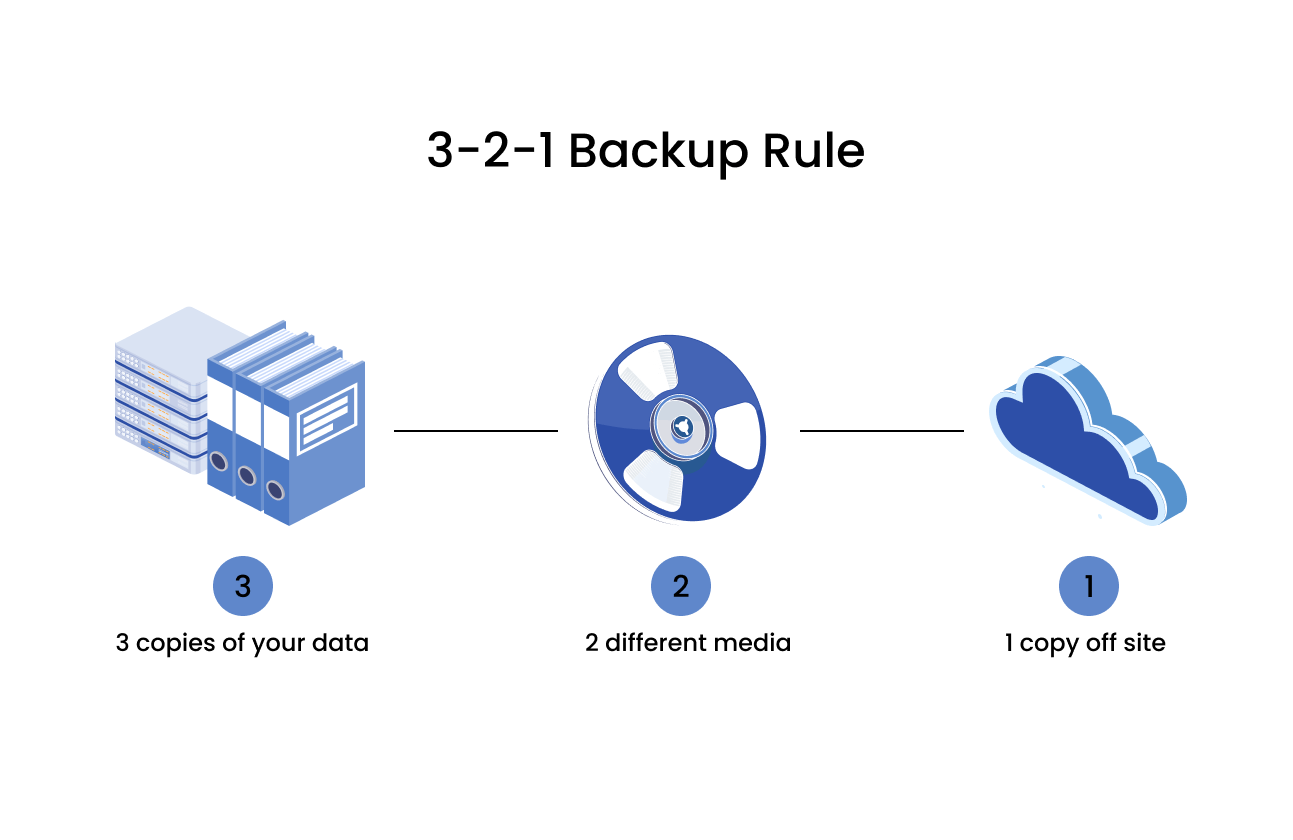
Data replication is the process of backing up data to an off-site location at regular intervals to abide by the 3-2-1 Backup Rule as discussed in the previous blog post. The backing up of data to storage devices is essential for quick recoveries from any intentional or unintentional complication.
Computer processing includes the additional feature of computation power in off-site locations. When any harm comes to the data or servers at the primary site, the computation can be handed over to these remote locations to ensure that the company thrives non-stop with no hassle. To highlight the significance of such a security measure, let us look into a quick case study.
On October 11th, 2021, Facebook had witnessed a massive outage that led to its servers going dark for over 6 hours. This meant that all of its applications such as Instagram, WhatsApp, and Facebook went down and were completely inaccessible. To understand the gravity of this situation, let us look into one particular mind-boggling statistic. The loss incurred by Facebook was a startling 60 billion dollars. Further, Mark Zuckerberg was subjected to harsh criticism and witnessed various users speculating theories behind the cause of such an incident. Adding on, investors had to place their trust on the stand and rethink their choices. A major repercussion however, was that companies that banked on WhatsApp for communication took a huge hit due to the disruption in connectivity, inevitably leading to multiple problems.
With a proper disaster recovery plan in place and provisions to compute off-site, the casualties could have been reduced drastically. Thus, disaster recovery wields great power in mitigating unforeseen disasters with ease and in an organized fashion.
Let us address the next big question,
What Is a Disaster Recovery Plan?

A disaster recovery plan is a formal and structured document listing the plan of action, the Disaster Recovery (DR) board members and their roles, the storage devices and off-site premises owned, various objectives to achieve, etc. Numerous components integrate themselves to constitute the DR plan, and a few of them are highlighted below:
- Identification of goals: The working of the DR plan balances on the goals identified as the objectives and timelines manifest around it.
- Identification of Essential assets: For the DR plan to remain economical, it is of primary importance to identify critical data that will undoubtedly have to be backed up.
- The DR team: Creating a DR team consisting of experienced candidates is essential for quick responses with minimal damage incurred.
- Inventory handling: With numerous storage mechanisms employed and different kinds of data involved, an inventory should maintain a detailed account of the same.
- Testing and Optimization: For the disaster recovery plan to provide a promising result, testing it relentlessly and optimizing it further is required. With an exponential increase in imminent threats and the advancement of technology, updating the strategies in place is essential for a fool-proof DR plan.
| Recovery Point Objective (RPO) | Recovery Time Objective (RTO) |
|---|---|
| The RPO measures how frequently backups should take place. It must account for the loss that may incur if any complication arises between the backups and its tolerability. | The RTO specifies the amount of downtime a company can afford to lose without a drastic adverse effect on its revenue. |
With a clear-cut understanding of the importance of Disaster Recovery, the need for tape storage surfaces. Off-site locations and even on-premise sites utilize tapes for their storage. Tape storages’ evolution over the years has led to a tremendous increase in its storage capabilities and its compatibilities with new technology, thus becoming the most reliable storage option.
From punch cards to cloud storage, data has witnessed a massive change over the years. With a rise in automation, contactless devices, self-driving cars, and the other marvels of technology, data storage has had its fair share of tremendous growth. For example, the lights-out data center.

What Is a Lights-Out Data Center?
A lights-out data center works with complete independence from any form of human intervention. With no humans in play, the need for light is redundant, thus giving rise to the name Lights-Out Data Center also known as the Dark Data Center.
Here are a few advantages that contrast Lights-Out Data Centers with its much brighter sibling, human intervened data centers:
- Human errors: The absence of humans offers resilience toward the errors made by them either intentionally or unintentionally, thus bringing it down to a bare minimum.
- Remote work: Staff and experts will have to carry out mandatory routine checks for maintenance with the added advantage of doing it remotely. Remote resource management and access to hardware help assuage the employees’ lifestyle.
- Absence of Oxygen: With the absence of oxygen, corrosion reduces, and the probability of a fire is non-existent. This enhances data security and offers a trustworthy guarantee to its clientele.
- Tape Storage: With tape storages’ magnification in terms of storage per unit, performance, and compatibility with earlier versions, tape libraries are used majorly in these centers. Thus, the countless advantages of tape storage tag along with it when used in lights-out data centers.
Another remarkable breakthrough in data storage is air-gapped networks. Let us first understand the term air-gap. An air gap is a security measure that isolates computers or peripherals from other devices and networks.
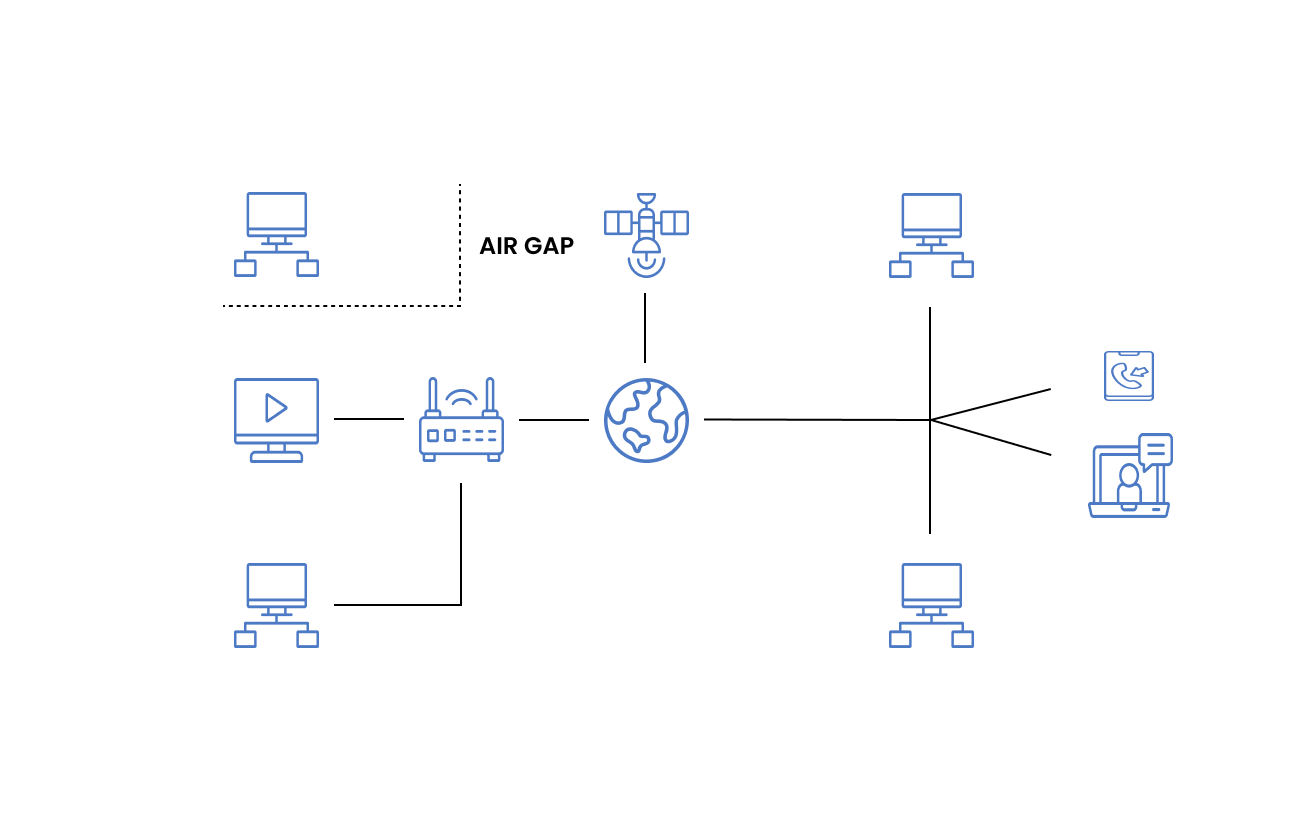
What are Air-Gapped Networks?
Air-gapped networks are secluded from other devices and insecure networks electromagnetically, electrically, and physically. Data transfer between devices of said networks will only be possible using USBs, CDs, etc. This invariably hardens access to the systems of the network and prevents unauthorized access and data transfer. Such limitations complement the network security and are thus highly sought-after for military and government purposes. A popular application of air-gapped networks is in black sites.
What is a Black Site?
Black sites are run by the military or government to carry out covert operations with an opaque communication between them and the citizens. These sites require utmost security and thus require a fool-proof data center for their sensitive data. Black sites are used by the Central Intelligence Agency, the CIA, to detain enemy combats and to carry out interrogations. Other use cases of black sites are seen in Warface research centers and the State Office of Information Technology Services. Warface research centers zeros in on developing tactical strategies, advancing the military force by harnessing technology, and is hence the hub for R&D. Thus, the involvement of the military and their regulations resulted in the need for communications secluded from the general public. Similarly, State Offices of Information Technology provide information technology and telecommunication services to government offices across the country, requiring highly secure networks. With an aim to develop a smart and efficient government through the centralized distribution of services and technology, there is an imperative need for secure networks similar to the working of black sites.
Zmanda has signed deals for data management in black sites in the recent past. Zmanda promises complete confidentiality and honors the trust invested in them. The black site data centers function completely offline and are isolated from the internet to prevent unauthorized access. Zmanda matches the security requirements through the provision of the below features:
- Air-gapped networks: As discussed above, air-gapped networks enhance security measures by eliminating ransomware and cyber attacks. Further, the Zmanda Management Console ensures that administrative work is performed with ease.
- Tape-Archival: Zmanda’s forte in tape backup and archival surpasses other competitions in the market. With years of experience and evolvement, Zmanda sticks with improving tape backup from the ground up to provide a cost-effective storage solution.
- Open Source Background: Zmanda’s foundation lies in its open-source software that enables its customers to view the code and customize appropriate storage format solutions pivoted on security.
Let us address a couple of other use cases highlighting the need for disaster recovery and optimizing the data storage solution using tape storage.
Enterprise Audits

Enterprises today possess numerous offshore and onshore accounts with multitudes of transactions and taxes levied. These activities are recorded and verified through audits to ensure fair practice in accordance with government-enforced regulations. This necessitated a data storage mechanism and a disaster recovery plan that offers the utmost security and privacy for company trade secrets and transactions.
The most prominent solution sought-after was the hybrid environment that offered its clientele simple data management practices and a reliable disaster recovery plan. Zmanda equips its clients with advanced enterprise protection with features and packages like no other. We constantly scale up to stay on par with the continual development of technology and demands.
Mission Critical Production Systems
Certain companies function with zero compromises on downtime and generate mission-critical data at regular intervals. These companies fall under the roof of Mission Critical Production Systems.

Data generated by said companies are called mission-critical data. The term mission-critical refers to any factor of a system essential to the company and whose disruption results in a tremendous loss in revenue, disruption of their activities, and an unfortunate hit on its reputation. There are various challenges tied to these companies. Below is a set of primary questions that a company should answer to ensure that the company has a proper mitigation plan in place.
- What data is mission-critical? => Identification of the mission-critical data, also known as critical data elements, is cardinal to ensure that the company suffers no loss during downtime and to lighten the cost invested in data backup. Blindly securing all data is a costly venture.
- At what time interval do I back up the data? => The time interval after which data backs up to the secondary storage is needed to ensure that data lost during this interval is in line with the Recovery Point Objective.
- What is my Disaster Recovery plan? =>The DR plan executed must be well structured and documented to prevent losses in revenue and enhance its functioning at all times. Personnel should be identified well in advance to facilitate their training and thus a quick recovery.
- How many replications of data do I need? N+1. N+2 …? => N refers to the primary data, and the + refers to the additional data replications that are in place. Depending on the data and its applications, backups must be secured in various locations or various numbers. This ensures a zero loss in backup and a fool-proof backup and management system.
Research

Scientific explorations and laboratories like CERN generate a colossal volume of data. Every experiment performed generates conclusions and theories that are recorded and studied further. CERN’s data storage relies heavily on tape storage. A consequence of a loss of such data is millions of dollars lost as these experiments and studies are carried out with utmost precision, heavy and complicated equipment, and with months of time invested. Thus, a disaster recovery plan and a backup system are key to sustaining data over a long period.
Health Care

A field of continuous burgeoning is health care. With an increase in technological marvels and healthcare equipment, the data generated must also be on par for optimum compatibility. Artificial Intelligence, Machine Learning, Neural Networks, etc, have seen a rise in their utility towards health care in terms of diagnosis and discoveries, resulting in the need for congruent data storage solutions.
Hospitals and clinics often opt for on-premise data storage to enhance control over internal data and thus improve security. Cloud storage or hybrid environments are used for backup and archival purposes. Moreover, healthcare data are tied to numerous regulations and standards to ensure client confidentiality and the harmonious working of the centers, which are best met with hybrid environments in compliance with the regulations.
The increase in clientele, research in health care, and loyal patients who visit over the years require data backup and disaster recovery plans. With hundreds of in-patients admitted throughout, healthcare centers must ensure they have data such as doses administered, etc, handy and backed up in the event of untoward disasters.
Tape storage saves the day once again, with its ability to store the influx of data at minimal prices without compromising on security and performance. Zmanda offers its customers just the same with a promise to honor it. Here is a real-life example of Zmanda’s wonders in the healthcare industry.
The countless applications of disaster recovery and tape storage have given rise to a set of standards to be followed, data compliance.

What Is Data Compliance?
Data compliance refers to the regulations and practices that should be necessarily followed to ensure uniformity and fairness. These legal requirements should be adhered, to ensure that the clients’ personal information is kept confidential and sensitive data and assets do not fall into the wrong hands. Data compliance, security, and integrity are all focused on minimizing threats to data and data handling risks. Various organizations oversee the drafting of these legal regulations to whom a company is answerable if found guilty of malpractice. Data compliance not only monitors the functioning of companies but also helps them gain the trust of their customers.
Thus, data compliance with the enforcement of transparent regulations is a quick way of developing a company built on customer trust and satisfaction, a true game-changer in today’s industry.

Disaster recovery, data compliance, air-gapped networks, lights-out data centers, and so on are necessary parameters to be accounted for in the long run for an effective and secure data storage solution. Further, technology is relentless in its growth, requiring a need for compatible and robust remedies. Zettabytes of data are accumulated over the years as today’s data is a fortune for tomorrow’s. With groundbreaking discoveries made every day, data obtained in 2022 will be worth millions of ten years down the lane. After all, ‘You have to know the past, to understand the future’ ~Carl Sagan.
Bearing in mind Carl’s wise words, protect your treasured data with Zmanda. Click here for a free trial with Zmanda, the royal treatment your data deserves in an effortless and highly secure manner.